![]() Guest Post: This article published with permission from our partners at DroneII, Drone Industry Insights.
Guest Post: This article published with permission from our partners at DroneII, Drone Industry Insights.
Drone data security is in a very early stage – not in terms of infrastructure and opportunities, but in terms of adoption. Now, let us paint the bigger picture and put drone data security into context.
Data security is always temporary – everything is secure, until it isn’t. IT companies find themselves in a constant cat-and-mouse game with those who proof existing security standards to be insufficient. The degree of connectivity increases at light speed, making the whole topic of data security in a highly-connected world hugely important and inconceivably complex.
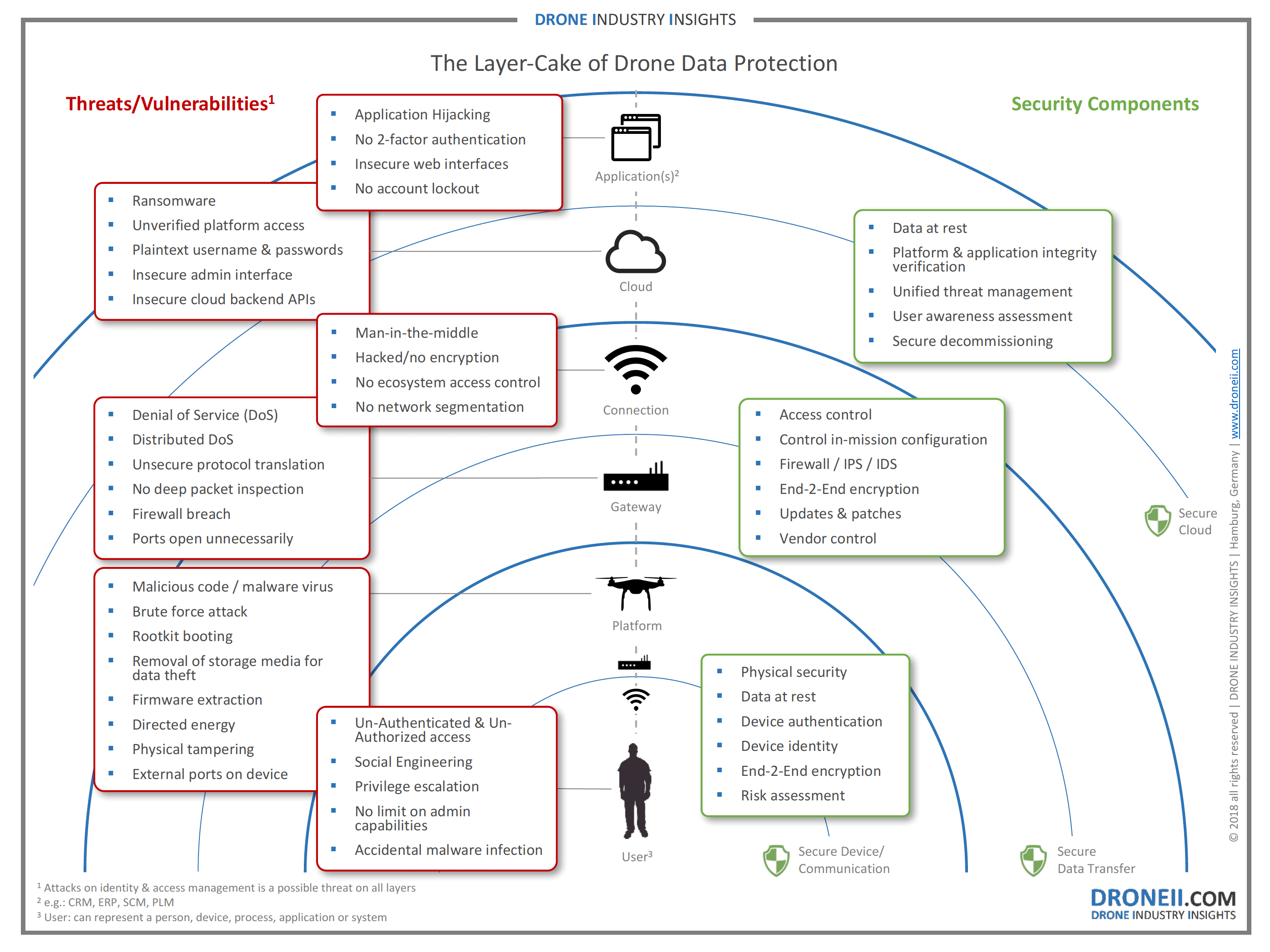
But let us start at the beginning and see what this means for commercial drones today and in the future. Drone data security is essential on three major levels: The first level considers the interaction between drone and user. The second and third level concerns the wireless data transfer and cloud storage. Transmitting large amounts of data wirelessly might still seem far from reality due to today’s bandwidth limitations, but that does not make data security less important for the future. “Security layers are important factors for drones’ success going forward. In fact, we believe it will be a critical enabling factor for the success of the drone revolution.” Oren Elkayam, Founder & CEO of Mobilicom recently underlined in an interview.
The Layers
Today level 1, the link between device and user is the only focus of discussion. For instance, the rather insecure link between user and device is used by counter-drone devices to stop a drone in-air or even force it to land, and there is already a great variety of non-physical counter drone (CUAV) solutions available. Greater drone data security provided by encrypted data-links help to reduce the risk to be hacked – in return, however, this also means an increased risk through encrypted rogue drones.
Layers 2 and 3 are just as crucial – in this case, the hijacking of the platform is not in the foreground but the wiretapping of the collected data. With increasing automation, however, this will also include the control of the platform. The list of threats is growing every day, making it essential to create an ecosystem that is secure and reliable.
Imagine the following scenario: you are sitting in an autonomous aerial taxi and ransomware forces you to transfer money to an account within the next 15 minute. If you do not comply, the platform will shut down the engines and make you crash over a highly-populated area. Especially when piloted aircraft become unpiloted, there must be extremely reliable safety mechanisms in place. From a programming point of view, it appears to be a thin line to make robots work efficiently and having all necessary safety nets in place at the same time. It is basically the same with commercial aircrafts today, where system redundancy is traded for payload and range.
Degree of Automation
Drones, just like aerial taxis will only be effective when they work at an extremely high degree of automation – this includes the ability to interact with other systems (e.g. air traffic management, weather forecast, etc.). The ecosystem for all that to happen already exists – it is called the internet (the internet of things or IoT, to be accurate), which is not necessarily a safe place for data.
Today you can control a thermostat via your smartphone – that is a classic IoT use-case. With an increasing level of automation, complex flying robots (like drones) will soon be just as easy to control. But according to which standards will they interact with other devices? How do you protect devices that could do harm to others when hijacked? This requires safety mechanisms on each level. The graphic above shows the main trust boundaries of drone data security (transition of data/info from one source to another) but our view forward should not stop here.
Artificial Intelligence
AI will boost automation! We are on the verge of a second industrial revolution. AI will be spread on the grid like once electric power. Everything that in the past got electrified will soon be cogni-fied. The AI train already left the station, full steam ahead and there are no brakes to pull. Today we are teaching machines how to think, how to understand our behavior and how to defend themselves. What could possibly go wrong?
Data scientists and developers will create the future of AI, but again – according to what rule-book? What standards are out there to respect when creating, what scientist claim to be the last big invention that humanity will ever need to make? What is the foundation of a world where smart robots will design and manufacture other robots? Personally, it feels a lot like chemistry class. We have nothing on hand but a few basic principles and a lot of elements in the equation, while we have absolutely no idea of what happens when we mix it all together and how to control it.
The Control Problem
To make sure this control problem is solved by the time needed, it is essential to work it out in advance. It might be difficult to solve the entire control problem from the start because many elements can only be put in place once we know the details of the architecture where it will be implemented. However, the more we consider these developments and try to solve potential control problems early on, the better the odds that the transition to the machine intelligence era will go well.
There are already many possibilities to safely and securely connect drones to the internet of things and we are only in minute one of the game. A lot of money is and will be spent on drone data security to trial-and-error the way forward. This, unfortunately, will include failures. New and very complex technologies are not always 100% safe from the beginning (e.g. self-driving cars) – we simply expect technology to do what it is supposed to do. And if the machine does not always know what that is, artificial intelligence will allow the machine to react to changing conditions.
If you now think that this is so far away and will not bother us for the next fifty years, try to look at it from a different point of view. The computer scientist Stuart Russell put it this way: Imagine that we received a message from an alien civilization, which read: “People of Earth, we will arrive on your planet in 50 years. Get ready!”
Do you think we would just sit here, counting down the months until the mothership lands? We would feel a little more urgency to work the switches. For the commercial drone market – the incredible melting pot of technologies – this means to truly think progressively and to better be safe than sorry, when it comes to drone data security.
Learn more about data security and the commercial drone industry on: www.droneii.com.

Miriam McNabb is the Editor-in-Chief of DRONELIFE and CEO of JobForDrones, a professional drone services marketplace, and a fascinated observer of the emerging drone industry and the regulatory environment for drones. Miriam has penned over 3,000 articles focused on the commercial drone space and is an international speaker and recognized figure in the industry. Miriam has a degree from the University of Chicago and over 20 years of experience in high tech sales and marketing for new technologies.
For drone industry consulting or writing, Email Miriam.
TWITTER:@spaldingbarker
Subscribe to DroneLife here.





[…] ที่มา: https://dronelife.com/2018/05/25/droneii-drones-and-data-security-a-progressive-look-into-the-future… […]