Examining the Cybersecurity Risks and Resilience of RTK Modules in Drone Navigation Systems
by DRONELIFE Contributor T. Seth Ford (Drone615, Nashville, TN)
Understanding the GPS and Space Economy Framework
According to GPS.gov, the official website for government information concerning the United States’ Global Positioning System (GPS), it is comprised of three segments: the space segment, the ground segment, and the user segment. To further expand on this conceptual design, in his book Terra Calling: Defending and securing the space economy, Stefan Soesanto describes the entire space management effort as a multi-domain, multi-sectoral, and multi-asset system within the greater space economy, grouped into five parts: 1) Space-based assets, 2) Earth-based control stations, 3) Earth-based communication stations, terminals, and devices, 4) Space industry, and 5) Space economy supply chain.
As more satellite-based components are outsourced to international manufacturers and commercial-off-the-shelf (COTS) options become mainstream, providing greater options for satellite operations, these benefits, however, come with new and expanded challenges in preventing and handling cyber attacks and downtime caused by unintentional environmental interactions.
RTK Modules and Their Role in sUAS Operations
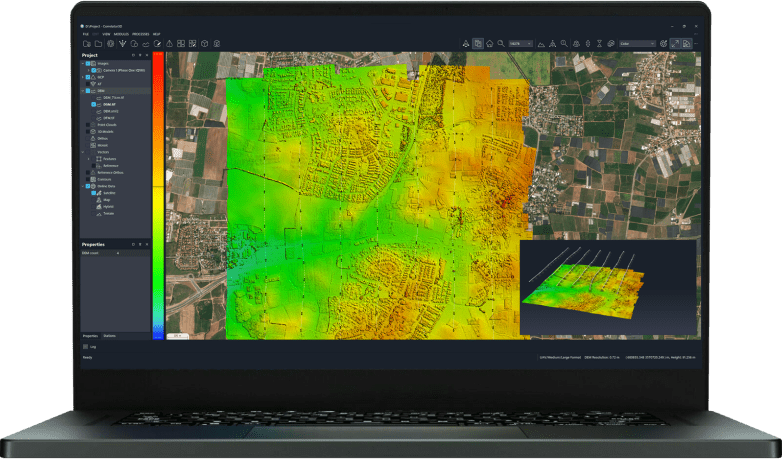
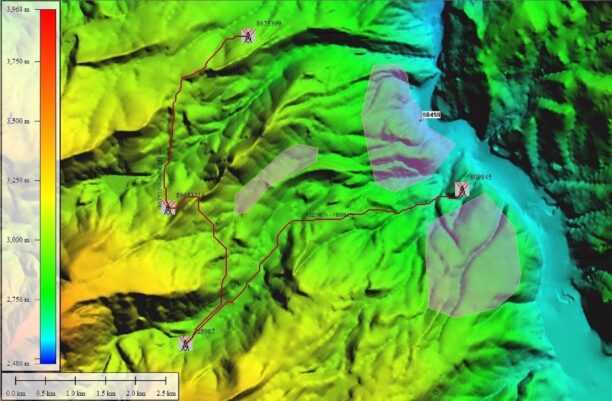
One such component utilizes real-time kinematic (RTK) differential positioning, combined with the entire Global Navigation Satellite System (GNSS), to enhance the positioning, navigation, and timing (PNT) capabilities of small Unmanned Aerial Systems (sUAS) during autonomous flight mode. We’re going to focus, briefly, on the differences between RTK modules and internally built GPS receivers during small uncrewed aircraft system (sUAS) operations when utilizing an RTK module as the primary GPS receiver for autonomous mapping missions.

RTK modules enable a higher degree of global (absolute) accuracy compared to the GPS receiver located within a typical enterprise-level commercial Air Vehicle (AV) body/frame. This is especially important for land development mapping missions, where global accuracy is just as crucial as relative accuracy.
Technical Advantages and Emerging Vulnerabilities
RTK modules can track multisystem satellite L1 and L2 civilian bands over code and carrier phase signals, which provides higher accuracy and more reliable PNT solutions with minimized impact from electromagnetic interference (EMI), as discussed by GNSS pioneer Dr. Jan Van Sickle in his 5th edition of GPS and GNSS for Land Surveyors (2023). However, RTK operates on RTCM 10403.3, aka version 3.3, as an open format and not restricted to a specific receiver type. This specific version was enhanced to allow communication with all GNSS constellations. This includes China’s BeiDou and Russia’s GLONASS systems.
While RCTM 3.3 is a major upgrade for commercial operations, it also presents potential increases in cyber vulnerabilities over shared satellite constellations. GNSS receivers are typically built into both the ground element (handheld controller) and the air element (air vehicle). Both can operate on specific constellations, either by design or by user settings, but RTK modules typically can connect with all four major constellations (GPS-US. Galileo-EU, GLONASS-Russia, and BeiDou-China) and are selectable with smaller, regional constellations. By default, the more available connection points, the greater the risk of potential attacks.
Spoofing, Jamming, and the Need for Countermeasures
In the case of accessing the RTK module to use the Air Vehicle as a deadly projectile instead of a mapping tool, one could spoof an L-band channel and inject false data into the PNT solution, causing the sUAS to give false location reports. Although there are just a few rumored and unconfirmed reports of criminal hacking specifically through an RTK module, however remote or improbable, the overall concept should be further examined. Of note, companies like GPSPATRON produce devices and software to measure, defend, and protect against jamming and spoofing attacks through counter-spoofing tactics.
Supply Chain Risks and Regulatory Gaps
Another front of attacks can come from RTK hardware embedded during the manufacturing process. In his 2019 article Cybersecurity Principles for Space Systems, Gregory Falco points out that penetration tests into a company’s virtual network often examine the manufacturing process supply chain for embedded code or product defects intended to destabilize or harm the end-product or related systems. Cybersecurity can legally be traced back to the efforts, or lack of efforts, as in the case of the Federal Trade Commission (FTC) v. D-link for inadequate cyber safeguards in 2016. The Original Equipment Manufacturer (OEM) can be held responsible for these faults, and should, within reason, but regulations and standards are almost non-existent or at least have been up until the late 1990s when the first cyberattacks targeted GNSS satellites. Since then, cybersecurity development has been largely reactionary, rather than proactive, in addressing issues and preventing future occurrences.
Balancing Benefits and Cybersecurity Needs
In short, RTK modules utilize more frequencies than conventional sUAS-built-in GPS receivers, offering enhanced reception capability and efficiency. However, these benefits may not adequately safeguard against cyber threats due to non-standardized interoperability protocols and limited third-party OEM vetting procedures. While the risk of GPS spoofing through RTK modules is minimal, these communication paths could be made more secure with higher levels of protection. Encryption, at the very least, safeguards data from unauthorized access and ensures the integrity and improved reception rates of the intended data packets for the intended user
 T. Seth Ford is a US Marine Corps combat veteran who flew attack helicopters and small drones in combat zones and assisted in small UAS testing and evaluation. Seth holds degrees, certificates, and licenses across multiple fields and disciplines and is currently seeking an MS in Uncrewed and Autonomous Systems at Embry-Riddle Aeronautical University. He is the founder and principal pilot of drone615.net in Nashville, TN.
T. Seth Ford is a US Marine Corps combat veteran who flew attack helicopters and small drones in combat zones and assisted in small UAS testing and evaluation. Seth holds degrees, certificates, and licenses across multiple fields and disciplines and is currently seeking an MS in Uncrewed and Autonomous Systems at Embry-Riddle Aeronautical University. He is the founder and principal pilot of drone615.net in Nashville, TN.
Read more:

Miriam McNabb is the Editor-in-Chief of DRONELIFE and CEO of JobForDrones, a professional drone services marketplace, and a fascinated observer of the emerging drone industry and the regulatory environment for drones. Miriam has penned over 3,000 articles focused on the commercial drone space and is an international speaker and recognized figure in the industry. Miriam has a degree from the University of Chicago and over 20 years of experience in high tech sales and marketing for new technologies.
For drone industry consulting or writing, Email Miriam.
TWITTER:@spaldingbarker
Subscribe to DroneLife here.





Leave a Reply