Hooray. It’s a new chapter in the ongoing spat between DJI and the digital security community. Although we don’t anticipate any Hollywood producers buying the rights to this one, it’s yet another interesting case of criticism and veiled references to a lack of technical understanding at DJI. Either way, it doesn’t look good for the industry’s leading manufacturer.
Over the weekend Department 13, a counter-drone technology company best known for its Mesmer platform, released a report highlighting various flaws in DJI’s AeroScope system.
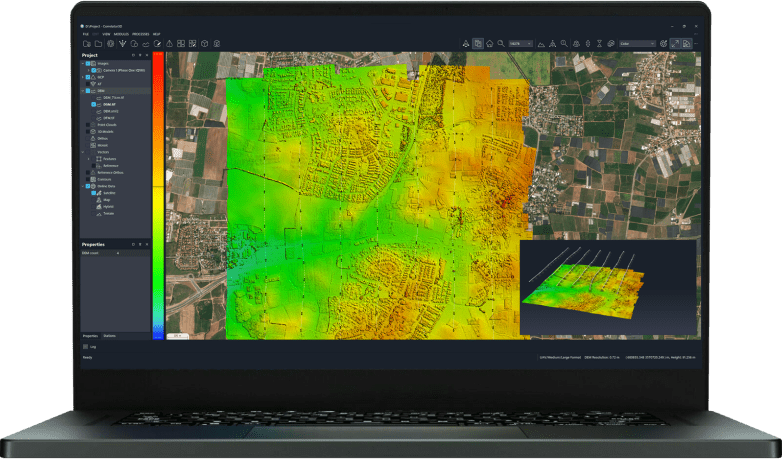
AeroScope is DJI’s first attempt to develop an easy way for law enforcement to remotely identify unmanned aircraft. As the manufacturer is thought to have made more than 70% of drones in the air today, it makes sense that they are taking positive steps to ID their aircraft.
The Context
DroneLife understands that this report was written several weeks ago, so shouldn’t necessarily be viewed in the context of the recently made-public bug bounty spat between DJI and Department 13’s Kevin Finisterre. Instead, it’s a first-impression account of Aeroscope from a technical perspective.
The Faults in AeroScope (According to Department 13)
We are not IT security researchers and won’t pretend to be. For that reason, we’ll let the folks at Department 13 explain the perceived flaws in AeroScope (which you can read in the report here.)
But in simple terms, the report suggests that Aeroscope is vulnerable to hackers – albeit sophisticated ones.
The first point made in the report is that “a savvy engineer could reverse DJI’s implementation for malicious purposes to spoof Drone ID beacons.” It’s easy to see how that might cause problems for those implementing the system at airports or sporting events.
There are further concerns raised regarding the vulnerability of user data, the privacy of pilots and the ability to turn off remote ID – particularly in light of the DJI jailbreaking scene.
The whitepaper reads: “several other security attestations have been made about DJI’s Drone ID implementation. These attestations include: “not something the user has a choice about turning on, or off”, “no issues with person perhaps complaining ‘now they are being tracked’”, “Tamper proof solution, because it is part of the C2 link”, “We can report… Unique ID built into the hardware to the user can’t change or spoof that.”
In the face of the DJI Reverse engineering, jailbreaking, and modification scene, some of these statements are questionable at best. When an end user jailbreaks a DJI drone, a number of these statements become immediately false. In other cases, the statements made are blatantly incorrect, and show a lack of comprehension of various internals of DJI’s drone platforms, as well as of general digital privacy concerns.”
DJI Responds
DJI has been quick to respond to the Department 13 critique, stating that “some counter-drone companies that see AeroScope as a competitive threat to their expensive products have deliberately distorted how AeroScope works and raised spurious objections to how AeroScope supports legitimate drone operations.”
DJI has suggested that the report was motivated by Department 13’s falling stock price in the wake of the Aeroscope unveiling, pointing out that the counter drone tech company sells “a $340,000 drone detection system with a $44,000 annual maintenance fee,” and that “DJI has not set a price for AeroScope, but it is expected to be less than $5,000.”
This is a strange parallel to draw, given that the Mesmer system has one pretty big distinction: it actively stops drones deemed as a threat. It’s not impossible to imagine a scenario in which both systems would be applied to protect sensitive locations and empower law enforcement agencies. It’s not a case of one versus the other; they perform different functions.

However, DJI also responded to specific points made in the report:
Privacy rights of drone pilots
Governments around the world have made clear they intend to soon require all drones to transmit some form of identification and telemetry information. DJI believes an important public policy debate is necessary to balance authorities’ legitimate concerns against the privacy interests of drone operators, as well as the burdens and costs that will be placed upon them.
The discussion about Automated License Plate Readers (ALPR) and government or private databases is also valid. However, the white paper by Department 13 envisions a possible long-term outcome no worse than various alternative remote ID solutions in which a “total awareness” system is not just a possible outcome, but the starting point by design.
Concerns about spoofing
First, there is a misunderstanding about the public policy assumptions behind drone remote ID. Remote identification policy, similar to UAS registration policy, presumes that most people want or will comply voluntarily with legal requirements and a means of compliance is presented to them that involves a fairly low burden.
Registration and ID solutions do not seek to stop the “bad actors” who will find ways to operate outside the system, just as a license plate system does not do anything to prevent people from removing, forging, covering, or stealing and swapping license plates. We have also heard from safety and security agencies that the goal for remote ID is to have a high percentage of drones identified, with an expectation that some drones will never be identified.
Second, to “jailbreak” a drone via software hacking is both a violation of DJI terms of use (because it compromises safety features) and also beyond the capabilities or interest of the vast majority of drone users. Those who would spoof their identification information in the face of a legal requirement would likely buy a non-ID-compliant brand or self-built drone anyway. Moreover, other remote ID solutions that allow drone users to provide ID information into a system will also be susceptible to some risk of spoofing, perhaps on a system-wide basis.
Third, once Remote ID is a legal mandate, there will be a back-end method, be it for aviation authorities or law enforcement agencies, to verify that the ID being transmitted is valid and corresponds to the drone pilot. This would be analogous to law enforcement officers verifying license plate and registration information on the road. Since there is no legal requirement for remote ID yet, it is premature for DJI and aviation authorities to implement a method to secure the remote ID mechanism. When remote ID regulatory requirements come into effect, DJI is confident that AeroScope will have the ability to adapt and meet the required security needs.
Ability to turn off parts of the remote ID information
The Department 13 white paper also points out that certain information in the remote ID transmission currently can be turned on and off by the user. This is by design, to allow DJI customers to make certain decisions about which data to broadcast in advance of a regulatory mandate. As with most technology, the pre-release, pre-regulation version will often differ from a final implementation version. Once a remote identification requirement is implemented by government, some of these user options will be removed so that the information required to be transmitted is in fact always transmitted.

Our Thoughts: The Role of AeroScope
There has been criticism of AeroScope in general, besides the technical flaws that leave it vulnerable to savvy engineers and hackers. A number of these flaws can be corrected but concerns remain over who should handle pilots’ registration data. It makes sense for this role to be taken by local, state or federal governments, not one company.
DJI’s Brendan Schulman told DroneLife that “We have no interest in handling the registration data. That can be entered by the customer, or handled on the back-end system run by the FAA that would connect a serial number or another unique drone identifier with the registration or pilot certificate information.”
One interesting point of debate centers around AeroScope’s inability to stop malicious actors. Although there haven’t been any high profile cases of weaponized drones in the US or Europe, it seems a matter of time before that threat becomes a reality. The ability to identify this kind of drone will be little help in a terror-related scenario.
Having said that, there is still a utility to identifying the drones that are authorized. “One of the purposes of a remote ID solution is to identify the drones that are authorized and not doing anything wrong,” said Schulman. “Then the authorities can focus on drones that are unauthorized, and take whatever steps may be necessary.”
DJI also points out – and they make a good point – that pilots with malicious intent will always find a way to operate outside the system, and that Aeroscope isn’t designed to stop them. Instead it’s targeted at hobbyists and works on the presumption that people will obey the rules – both with regards to registration and no-fly zones.
The bigger question is how useful this type of ‘situational awareness’ really is. There’s an argument to say that being aware of a situation unfolding say, at an airport, is pretty pointless if you can’t do anything about it. But it’s for that reason that Aeroscope would best be deployed near sensitive locations alongside counter-UAS systems.
Aside from that, there’s value in a system that can boost accountability among pilots and empower law enforcement to act, even if it’s after the fact. As seen in the video above, Aeroscope immediately gives enforcement agencies a way to contact the pilot (providing they’ve registered) and open up channels of communication. Let’s also not forget that this is a first iteration of a technology nobody else has put forward yet.
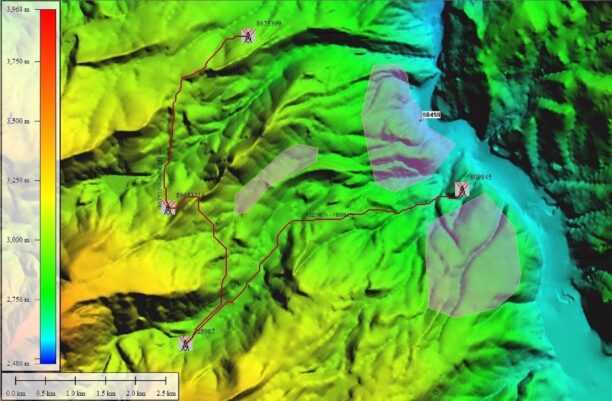
Speaking to DroneLife, security researcher David Kovar said that AeroScope could also provide evidence on drone flights and no-fly zone incursions. “I think it would be very helpful to deploy them in “identify only” mode to gather hard data on what UAV operations, if any, are occurring in various areas. Lawmakers could enact laws based on empirical evidence rather than fear and guesswork.”
An Update From DJI
Malek Murison is a freelance writer and editor with a passion for tech trends and innovation. He handles product reviews, major releases and keeps an eye on the enthusiast market for DroneLife.
Email Malek
Twitter:@malekmurison
Subscribe to DroneLife here.





[…] post Department 13’s Critique of Aeroscope & The DJI Response appeared first on […]